Wed:
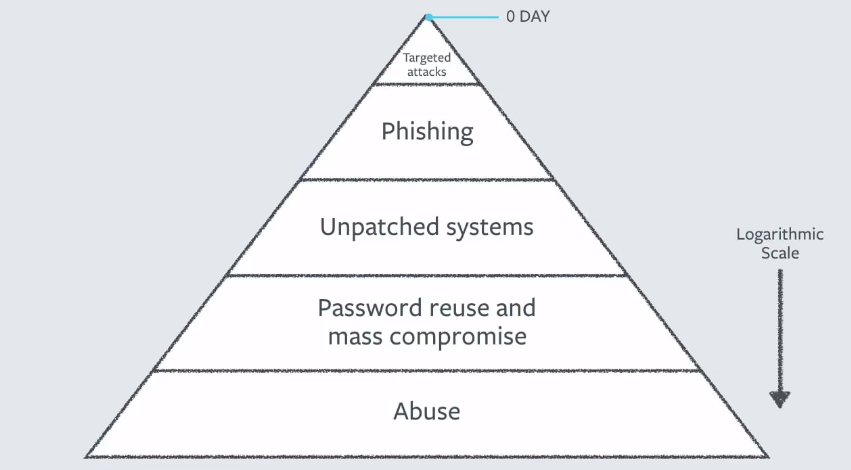
Keynote: The Keynote this year was Alex Stamos the Chief Security Officer from FACEBOOK. The main themes of his talk were collaboration in the industry, inclusion and diversification of everyone and anyone into the Security Field, and getting involved. One of the highlights was a pyramid visual he used to show how most threats in security are the mundane things like patch management, password management, and basic phishing techniques.
The smallest sliver was 0 Day type attacks, but they get the most attention. Security is still the same as it was 10 years ago, defense in depth. His keynote is available here starts around the 30 minute mark.
Orange is the new Purple – Aprils talk about integrating more security discussions into the Software Development process. Having Red/Blue teams engaged into the process so things like security, logging, and policy recommendations can be applied. It was a great talk and an important piece of building products with security built in and not as an after thought. I worked with April at Digex back in the day and am happy to see all the success she is having. She is one of the great minds in the Security Field. Follow her on twitter.
Splunking Dark Tools – A Pentester Guide to Pwnage Visualization – Pentest framework (DARK TOOLS) which is built in python on top of docker containers to allow Red Teamers to run against thousands of sites/targets easily. Docker architecture allows it to use more resources and multi-thread work. Framework is easily extendable. This takes a lot of the heavy lifting out of the first phases of pentesting. The way the data is sent into SPLUNK and the visualization provided are of huge value. I encourage anyone involved in Red Team activities to check out this tool and follow Bryce here.
and on Github: https://github.com/TweekFawkes
Hacking Server less RunTimes - I sat in on this talk for the first half hour. The main thing they showed was there are issues in AWS/Cloud environments but they aren't in the infrastructure but what type of code is deployed in the environment and how IT can be exploited. Example they used was a python script with an old/vulnerable library being used that gets called remotely and executed. Highlighting the fact that any code which is deployed into a production environment needs to be QA'd and checked for vulnerabilities.
Vendor Hall - Spent some time walking around the vendor hall. As the manager of the R&D teams i need to keep an eye on what the trends are in the industry and where we are heading in the near future. The main themes from this year are: Proactive hunting, EDR, machine learning, and behavior Analytics. Each of these sound great but are very involved pieces of the security puzzle. To utilize machine learning and/or behavior analytics you need to define your implementation strategy and have realistic SET goals on what you are trying to accomplish with this technology. Machine learning and Behavior Analytics have huge possibilities in security and in many other areas that will affect our daily lives but from what i saw in the hall we still have a ways to go. Once organizations start building more work process around ML/BA it will be another few years before we see the fruits of these labors.
What they’re teaching kids these days - Interesting presentation about the different tracks that are offered to College kids when it comes to security. Most of the standards are set by NSA. You can read more about it here: www.nsa.gov/resources/educators/centers-academic-excellence/cyber-defense/
Zero Days, Thousands of Nights - Good talk by Lillian Ablon . Interesting research around more than 200 zero day software vulnerabilities and their exploits. She went on to discuss the need to undisclosed vulnerabilities and how different nation-states will use these in good and bad ways. Truth of the matter, there will ALWAYS be undisclosed vulnerabilities and the related zero-days.
Pwnie awards - https://pwnies.com/pwnies.com/ Went to the annual pwnie award ceremony Wednesday night. It's a fun atmosphere with awards for achievements and failures of security researchers and the security community. My favorite category was the Best Song... Here were some of the creative nominees: Dual Core, MC Hackudao, Hello (Covert Channel) , Hacking in Song, Machines in Loving Disgrace. The last one was actual created by turning the malware of the last 20 years into song, converting it to audio...
Thurs:
Epocholypse 2038: What’s in Store for the Next 20 Years - Great talk by Mikko talking about what we will/could see in the next 20 years of security. One concept he discussed was when EPOCH will run out in year 2038 (03:14:07 UTC on 19 January 2038 to be exact). It similar to the Y2K issue we had which caused a lot of fuss but the world kept on spinning :) He also discussed allowing machines to make decisions without human interaction, programs writing programs, and how hard it will be to stop some of these things once they are started. The next 20 years in Security will be VERY interesting, we all need to be diligent to hold each other accountable.
Advanced Pre-Breach Planning: Utilizing a Purple Team to Measure Effectiveness vs Maturity - Presentation around more coordination between Red and Blue Teams when doing assessments. Allowing the teams to discuss the goods/bads/uglies of the engagement with the customer and providing useful strategies to change how they handle IR. One important concept he discussed was watching the OPS team while they are working an incident from detection to remediation and seeing how the Analysts think through what they are doing. Moving away from Run Books in a Binder format to having these types of documents embedded into the IR tools the teams are using. You should still have a Crisis Management Plan this is the last level of defense when the sh** is hitting the fan. This worst case scenario, power is out, systems are unreachable, etc.
Go to Hunt, Then Sleep - This was my favorite talk of the conference. Rob Lee and David Bianco do a great job discussing Threat hunting in the form of a children's story. It's available here: speakerdeck.com/davidjbianco/go-to-hunt-then-sleep The main theme of the talk is you need a PLAN to HUNT, it's not a random process to hunt for threats. I like the mention of using PCR (Producer-Consumer Ratios) it took me back to my days of working with Network Flow information. Give the preso a read!
Quantifying Risk in Consumer Software at Scale – Fuzzing - Presentation around coming up with a way to Quantify products with a Risk Score. Lot's of discussion around the different apps and platforms, the use of fuzzing techniques. It's an interesting theory but VERY hard to implement. And the team presenting is having a hard time with resources getting it going. if you want to help give them a shout: https://www.blackhat.com/us-17/speakers/Sarah-Zatko.html
Exploit Kit Cornucopia - Fun presentation on different Exploit Kits. Presenters went through a few Exploit Kits and how they communicated using legitimate sites(and Ad Servers). Good advice on paying attention to the URL patterns of these kits, looking for userids embedded. Good site for tracking EKs: ektracker.com/
Lies, and Damn Lies: Getting past the Hype of Endpoint Security Solutions - Great presentation on Endpoint Security Solutions (AV/EDR/etc). The presenters Lidia Giuliano and Mike Spaulding have done extensive testing on multiple products and highlighted the limitations in those products. The biggest take away is a lot of security products are NOT one size fits all, as a consumer you need to know what problem you are trying to fix and what tool will work best for that problem. Lidia/Mike have made the framework for testing these products and if you are responsible for purchasing decisions at your company you should use this information. (Update: here is the github repo: https://github.com/pinktangent/Endpoint-Testing )
Adventures of AV and the Leaky Sandbox - The last presentation i attended at BH. The presenters showed how they could ex-filtrate information from an endpoint through the cloud-enhanced AV product. Essentially the malware is written to encapsulate the exfil'd information within the 'rocket'. Once the piece of malware is run through a cloud AV/Sandbox environment the exfil'd information is unpacked and communicated to the system of the malware writers choosing. An interesting way of looking at getting information out of a 'closed' network/system. Brings up concerns of utilizing cloud based AV/Sandbox technology without proper vetting. If you are using cloud based AV you should look into this talk and verify with the vendor they are not vulnerable to this type of technique.
As always Blackhat was a great time. We are all battling the same issues and this conference allows us to collaborate and share our problems/solutions to make this world a better/safer place!
Good seeing everyone from the Old DIGEX and SILENTRUNNER crews!
Till next time!
Next on my conference agenda is RFUN (www.recordedfuture.com/rfun/ )
Bartlett



 RSS Feed
RSS Feed
