Day 1
Keynote:
Eric O'Neil keynote about current security threats. Ransomware being one of the bigger threats we are facing today. He shared a story about how they took down Hanssen who was selling American secrets to the Russians. (read more about it here>
Complement to Attack Method -
Talk was around building a standard for Playbooks/Workbooks for automation. So no matter what type of platform you are using you could apply the playbook from other tools (Phantom to Cybersponse, Threat Connect, to SIEMPlify).
Takeaways:
- Good sites
- http://www.threathunting.net/ - Good starting point for getting into Threat Hunting.
- CAR Mitre - Cyber Analytics Repository (CAR)
- OpenC2 - OASIS Open Command and Control (C2) - Creating a standardized language for the command and control of technologies that provide or support cyber defenses
Building an IR Plan that your Organization will ACTUALLY USE! - Kelly McCracken - Salesforce
Discussed how Salesforce manages their Incident Response and laid out some great advice about building teams and collaboration.
Takeaways:
- Define your IR process
- PRACTICE! Your organization needs to run through your IR process BEFORE there is an actual incident.
- Scenario Planning; Brainstorm different scenarios(Outage/Exploit/etc) and define what/who/how.
- One Message up to Management. Define WHO is sending the message so you don't have multiple messages going to Management from multiple people.
- Representatives - Define who the point/representative is from each involved team. Know who is the 'authority'/Incident Commander
- Define Notifications:
- internal -
- Develop Communication matrix
- Who is involved? team/personnel
- When will notifications be sent?
- By who?
- When will updates be sent and how?
- External
- Check contracts for what is required for notifications to customers/clients.
- Who approves the notifications?
- Who develops the notifications?
- internal -
IR Preparation - Continuously Assessing Global IT Assets - Mark Butler CISO Qualys
Discussion around tracking your assets whether they are on-prem or in a cloud architecture. Tracking and understanding threats against assets and what threats to worry about is paramount.
Takeaways:
- Understanding Vulnerabilities in current environment and the ability to understand the RISK to current assets is vital to getting the correct patch/update out at the right time.
- Asset management is crucial to security. if you don't know what you have you are open to a HUGE level of attack and uncertainty. Need to be able to understand active exploits to what assets are at risk.
- Need to monitor for changes in environment, new assets, changes to asset, etc.
Day 2
Keynote
CyberSecurity IR Social Maturity Handbook Discussion
Presentation around teams, communication, and collaboration. The speaker and his team have researched the importance of communication and collaboration within a CSIRT atmosphere. The handbook link is below. I recommend if nothing else reading the Executive Summary of the Handbook. Lots of great information and exercises to try with your teams.
Takeaways:
- Copy of the handbook here: http://tinyurl.com/CSIRTeamworkRegistration
- Hold weekly discussions with teams to discuss scenarios and how they were handled and identify ways to improve the tools, techniques, communication, and process.
- Have a way to share 'what folks know' in the organization so teams know where to go for Subject Matter Experts and/or for help.
- Take time to build the team. Trust can go a long way during an incident.
- There is a workshop coming up in Arlington VA Nov 16th:
Accelerating Analysis with Decision Trees - Rodney Caudle
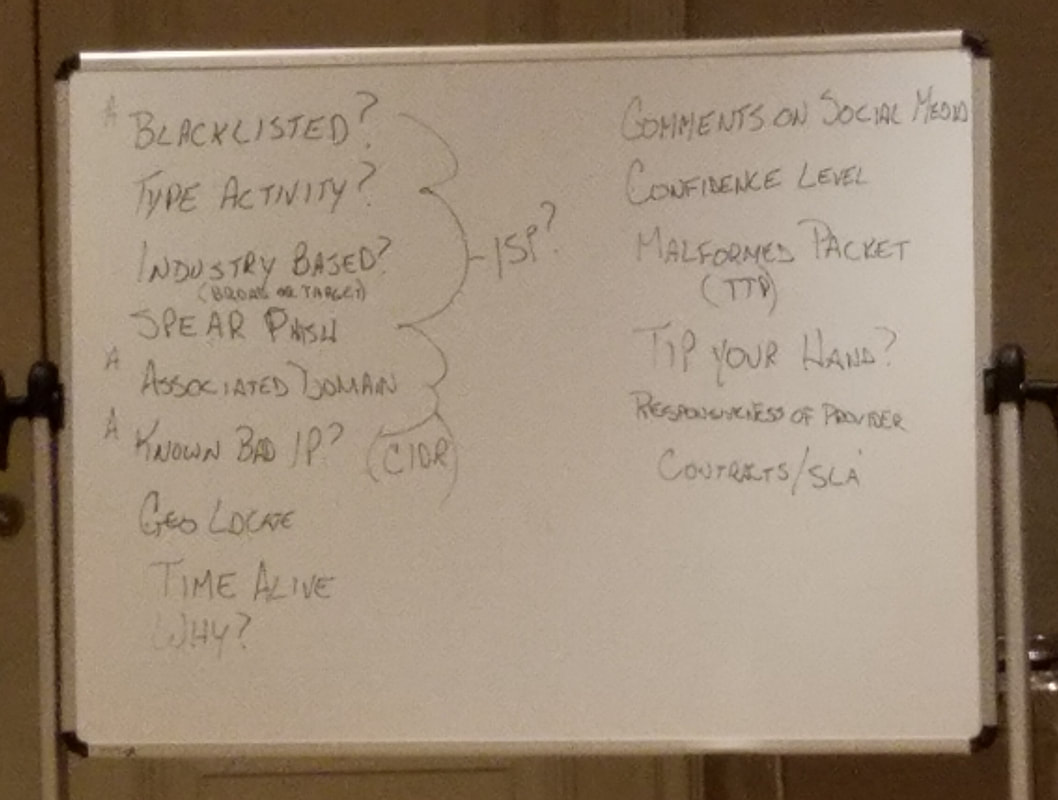
Great presentation on some of the research Rodney has done using Decision trees to help with Incident Response. Using Root Nodes and Leafs Nodes in a tree to walk through the specific questions which need to be answered, WHEN, and the choice/decision. The class was really collaborative, at the end we did a white board exercise discussing a decision tree for blocking traffic from an attacking IP. (image at bottom of page)
Takeaways:
- Brain storm with your team/organization for different scenarios threat/security/etc and start talking through a decision tree. It's a great whiteboard activity and you will find holes in your tools/process/techniques which you can improve on.
- Decisions trees are a good way to document what you would like to do in an Automation Platform.
- Rodney's SANS paper is available here: www.sans.org/reading-room/whitepapers/incident/investigative-tree-models-33183
- Create an Objective Statement for playbooks (what/why) to explain what it is used for an value. So you have an easy way to communicate the overall goal of the playbook. it's also a nice way to define things in layman's terms so anyone from the Sr Analyst down to the Intern can understand what it is doing and why we need it.
How do I know my SOC is ready for Automation - Karlo Arozqueta
Discussed some of the steps from: Carson Zimmerman book on building a SOC:
- Schmoocon talk: https://youtu.be/u4Zxk6WeVio
- Ten Strategies of a World-Class - Cybersecurity Operations Center Book
Takeaways:
- Use different tools to tests your security posture. One type of tool:
- Verodin - Attack automation to audit people, process, and procedure
- Do not forget to do things manually every once in a while even if there is automation. Need to be able to use the tools if automation platform/process breaks.
- Teach new analysts a task not a tool. if they know how to accomplish a task they will pick up the tools and techniques along the way and become a productive member of the SOC faster.
- Don't be afraid to let folks go if they are not producing, nothing worse than a poor analyst training a new analyst. Poisoning the well.
- Make your star Analysts mentors, allow them to train and help new hires. Don't pair your new hire with someone with 'spare cycles' because they might not always be the best for training. Aim for the most productive folks.
- Define metrics and revisit them over and over again to make sure they are the 'right' ones and are showing showing you the good/bad/ugly.
- Train your folks! Get multiple people trained up on your tools/technologies. Spend the money!
- Use Food and Activities to build your team togetherness/trust.
Effective Use of Threat Intelligence to Speed Incident Response
Travis Farral
High level discussion about the need for Threat Intelligence in IR. Also the inclusion of the Intel team when doing IR.
Takeaways:



 RSS Feed
RSS Feed
