|
Was lucky enough to see a few emails come through my inbox which pointed to some web sites serving up some Blackhole Exploit Kits..
0 Comments
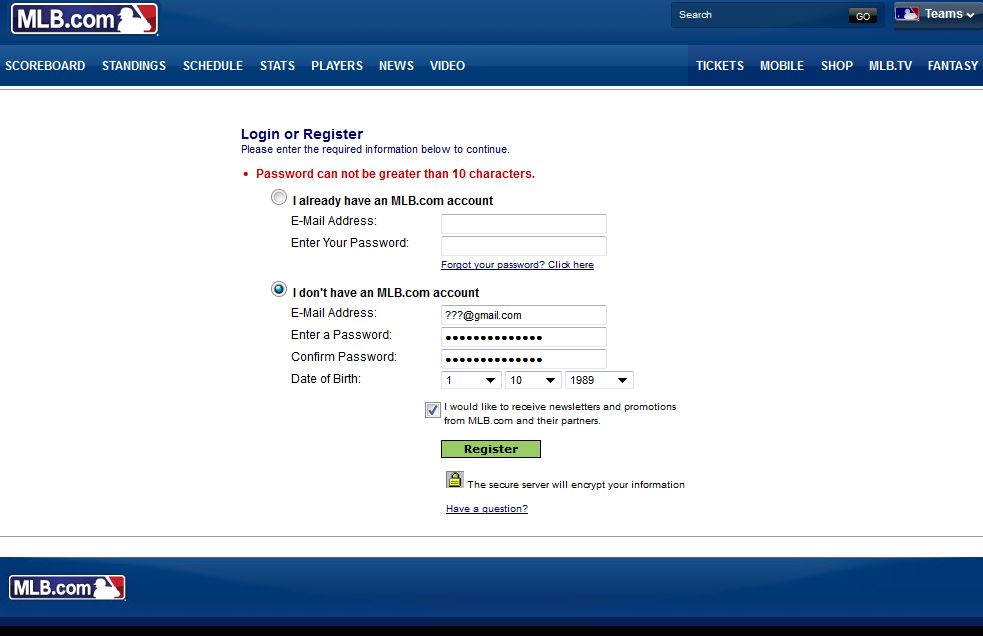
So I decided to buy the MLB.TV package this year for baseball season. I'm a huge NATS fan and like listening/watching to the games while at work if possible and thought this would allow me to do that. One thing that surprised me while creating an account was the Password limitations.
First I tried a password like this: 1122word991% And it complained about the 'special characters' Second I tried this password: 1122word991 And it complained that the password was too long and "Password can not be greater than 10 characters". It amazes me in this day and age that a website would have a limited password complexity and length policy. Just glad I didn't store my Credit Card # with my account. With easy Password Policies I wonder how often MLB fans have their accounts cracked... (BTW this isn't my email addy below :^P ) mab Did a blog for work about the DNSChanger Malware.
http://www.1901group.com/malware-dnschanger/2012.03.05 Doing a few talks on Security for the company I work for... Here are the notes I provided for anyone 'new to/or interested in' the Security Field: READ!!!
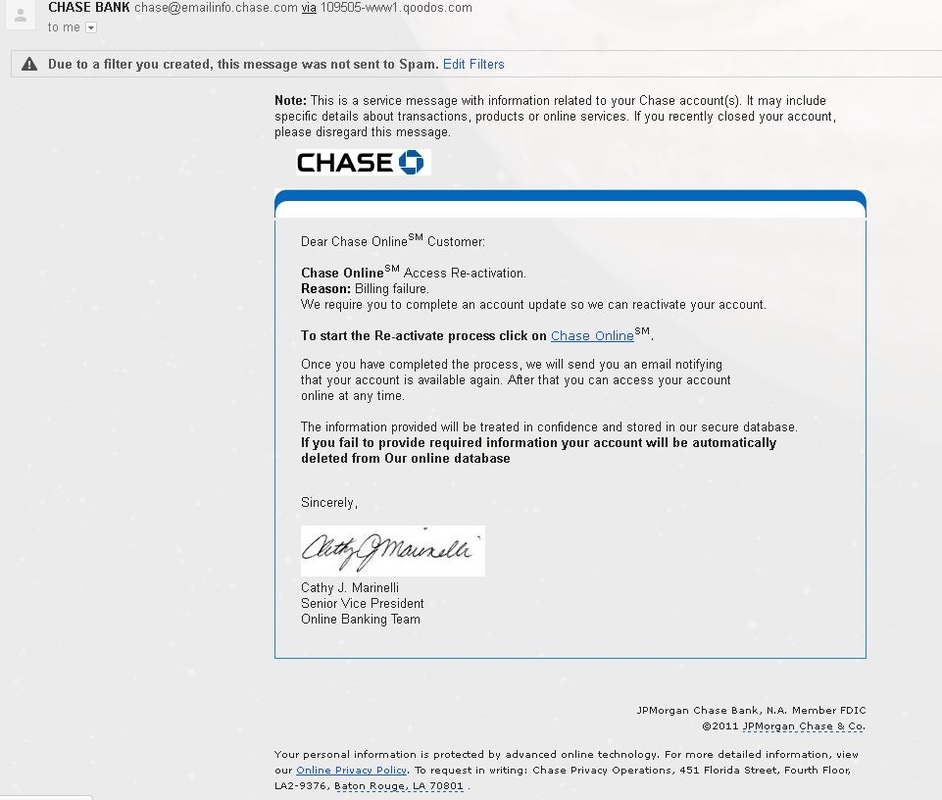
I am doing a security training for some folks next week and while putting together the presentation I did some 'movies' of different security/'hacker' tools in use: NMAP Example: (Attacker running NMAP on TOP, Target host with TCPDUMP running on BOTTOM) Nessus Example: (Attacker running nessus on TOP, Target host with TCPDUMP running on BOTTOM) Medusa Example: (Running Medusa against a Server running SSH) Backtrack - Metasploit Example So, I received an email from "Chase Bank" a few days ago... If you read the email above there are a few things that are funny about this email:
When I enter the URL in the browser a few things happen: 1. The Firefox Browser I am using was nice enough to tell me this has been reported as a 'bad' site. I skip the message to show what the site looks like. 2. The site appears and shows a site EXACTLY like the 'real' chase bank site. Notice the following in the video. The URL on the site is NOT related to Chase Bank (one strike) The page is being served over HTTP NOT HTTPS, any banking site will be using HTTPS for anything related to login and account information. (second strike) Everything looks identical to the chase bank site. When I hover 'over' the log on icon/button notice it is 'calling' a php file from the server. This tells me the login is storing data on the malicious server. (strike 3). So behind the scenes you enter your UserID and Password into this page it will save this information and either sell it on the black market or try and use this information to login to your account and do some bad things to your $$. All other links on the page are redirected to the 'official' Chase Bank Page. Be safe out there. DO NOT click on links in emails, documents, or IM without vetting them properly. Just another reminder to not TRUST ANYONE when it comes to emails:
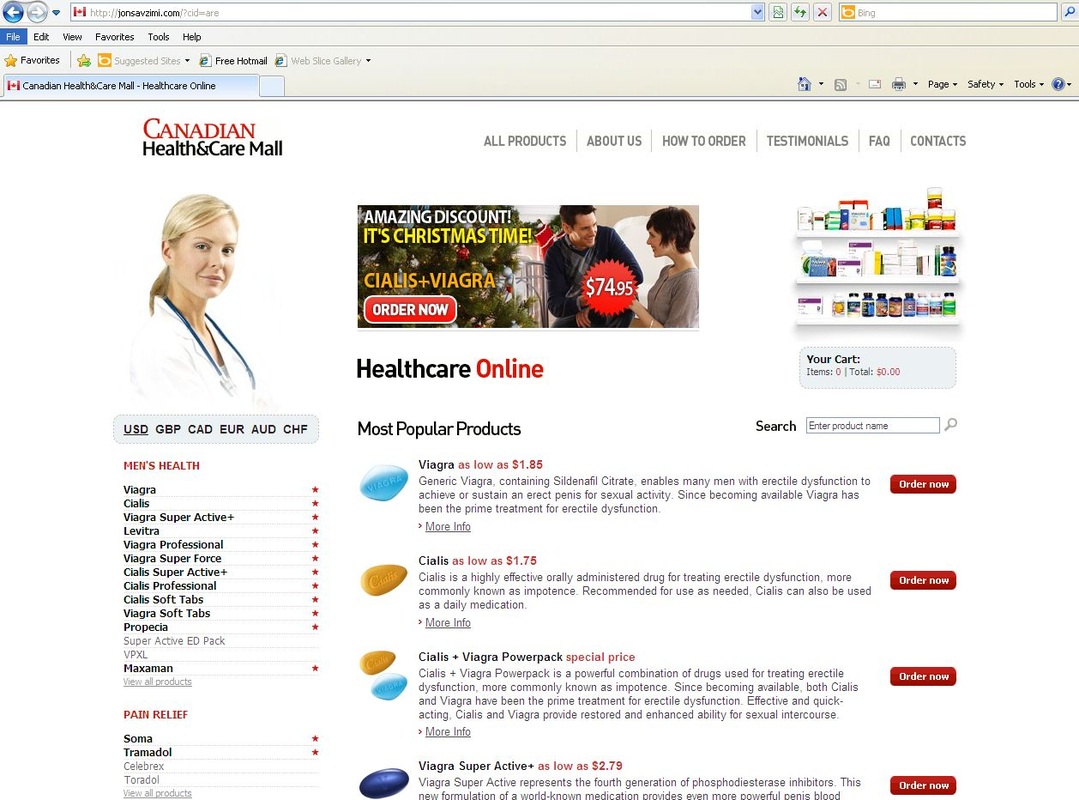
http://nakedsecurity.sophos.com/2012/01/10/fdic-malware/?utm_source=feedburner&utm_medium=feed&utm_campaign=Feed%3A+nakedsecurity+%28Naked+Security+-+Sophos%29 ASP.NET Patch - Exploit in wild - PATCH YOUR SYSTEMS - if you do NOT have automatic updates turned on, TURN THEM ON! http://www.net-security.org/secworld.php?id=12192 A friend of a friends email account got 'hacked' over the holiday and they sent me the spam the account was now sending out. It looks like this: ______________________________________________________________________________ From: <REMOVED> To: <REMOVED> Cc: Date: Tue, 27 Dec 2011 09:16:59 -0500 Subject: 1144444.927 hi, nice day hXXp://sebastienlarousse.teria.org/offer/newOffer.php?ekjprofiles=10 _______________________________________________________________________________ When I visit the link in my lab I am redirected to: hXXp://jonsavzimi.com/?cid=are Which looks like an on-line Pharmacy, where you can buy all the goodies; viagra, cialis... Did some researching on the site: http://www.ip-adress.com/whois/jonsavzimi.com
It's using 2 names servers: ns2.medicalpillshiv.com - which appears in multiple on-line malware analyzer reports. ns1.uvqip.ru - which also appears in multiple on-line malware reports. My advice when something like this happens to your account: 1. CHANGE your account password!! Then at least someone can't send emails directly from your account. (There are other ways to use your email address without having access to your account in some SPAM campaigns but that's another blog all together) Also look into enabling the 2-step verification 2. Take your machine off line and run an up-to-date ROOT KIT scanner against it. This will give you a good indication on whether your machine has some nasties installed on it. (The 'bad guys' might have brute forced the password on your 'on-line' account, but worse you could have a keylogger installed on your machine which has grabbed your password for the account and forwarded it out..) Here are some links for root kit scanners: http://www.sophos.com/en-us/products/free-tools/sophos-anti-rootkit.aspx , http://support.kaspersky.com/faq/?qid=208283363 Remember to change your on-line account passwords often and use STRONG passwords (here is a good video on creating passwords: http://youtu.be/Ah3gCnTi8b8) Check your SENT FOLDER periodically to double check emails are NOT being sent from your account which you have NOT sent yourself. And as always, KEEP YOUR MACHINE UP-TO-DATE with PATCHES (Operating System and Applications!) PS. I'll be updating this blog once I analyze the network capture associated with this traffic. mark __Wrote a quick BATCH file (because Windows was all that was available) to use TSHARK to parse through some capture files. The script below will parse out DNS info, HTTP information, IP Stat Information, TCP/UDP Information, and Protocol Type Information. The batch when run will create a Directory (using the filename) and create the output files in the created directory...
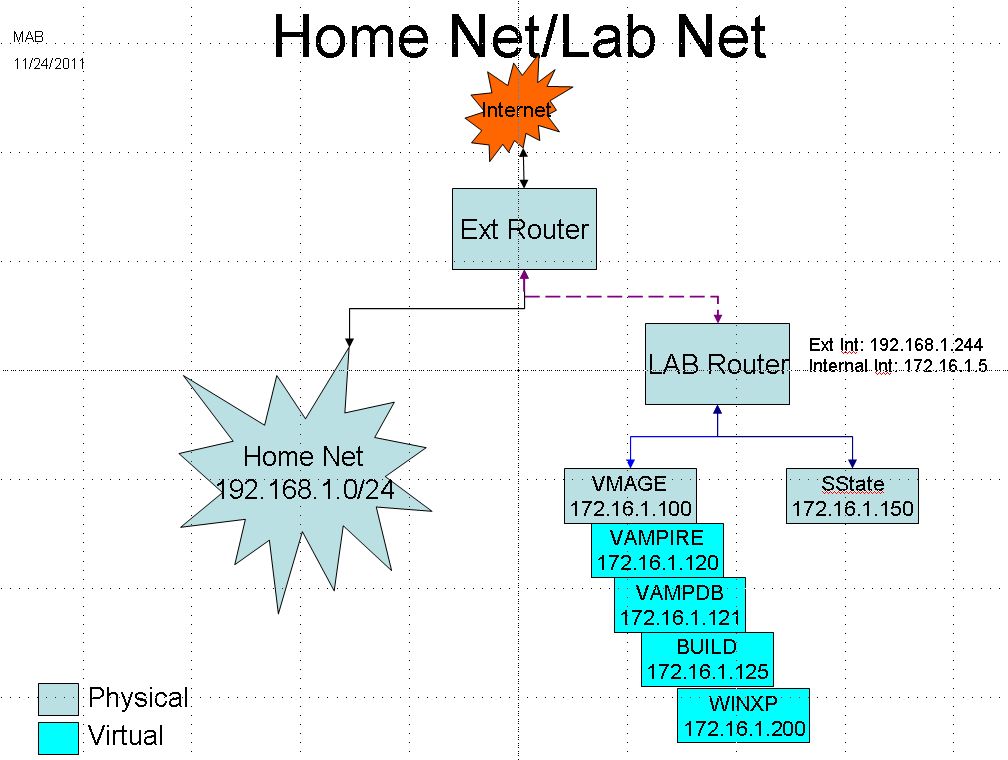
:: usage: tshark_ALL.bat <FILENAMEOFCAPTURE>.pcap @ECHO OFF echo "###########READY TO PARSE#########" echo "#######CREATING OUTPUT DIRECTORY######" mkdir %1_DIR echo "########Running DNS Extractions######" "c:\Program Files\Wireshark\tshark.exe" -r %1 -R "udp.port == 53" -T fields -E separator=# -e frame.time -e ip.src_host -e ip.dst_host -e ip.proto -e dns.qry.name > %1_DIR\dnstraffic.%1.txt echo "#######Running WEB Extractions######" "c:\Program Files\Wireshark\tshark.exe" -r %1 -T fields -E separator=# -e frame.time -e ip.src_host -e ip.dst_host -e ip.proto -e tcp.srcport -e tcp.dstport -e http.user_agent -e http.request.method -e http.host -e http.request.uri > % 1_DIR\httptraffic.%1.txt echo "#######Running HTTP REQUEST Extractions######" "c:\Program Files\Wireshark\tshark.exe" -r %1 -T fields -E separator=# -e http.host -e http.request.uri > %1_DIR\http_requests.%1.txt echo "#######IP STAT FILE CREATION#### "c:\Program Files\Wireshark\tshark.exe" -r %1 -q -z ip_hosts,tree > %1_DIR\ipstats.%1.txt echo "#####TCP CONVERSATION FILE CREATION#### "c:\Program Files\Wireshark\tshark.exe" -r %1 -q -z conv,tcp > %1_DIR\tcpconvo.%1.txt echo "#####UDP CONVERSATION FILE CREATION#### "c:\Program Files\Wireshark\tshark.exe" -r %1 -q -z conv,udp > %1_DIR\udpconvo.%1.txt echo "#####ETH CONVERSATION FILE CREATION#### "c:\Program Files\Wireshark\tshark.exe" -r %1 -q -z conv,eth > %1_DIR\ethconvo.%1.txt echo "#####Protocol Types CONVERSATION FILE CREATION#### "c:\Program Files\Wireshark\tshark.exe" -r %1 -q -z ptype,tree > %1_DIR\ptypes.%1.txt echo "#####HTTP INFO FILE CREATION#### echo "#####HTTP TREE SECTION####" > %1_DIR\httpstats.%1.txt "c:\Program Files\Wireshark\tshark.exe" -r %1 -q -z http,tree >> %1_DIR\httpstats.%1.txt echo "#####HTTP REQUEST TREE SECTION####" >> %1_DIR\httpstats.%1.txt "c:\Program Files\Wireshark\tshark.exe" -r %1 -q -z http_req,tree >> %1_DIR\httpstats.%1.txt echo "#####HTTP REQUEST TREE SECTION####" >> %1_DIR\httpstats.%1.txt "c:\Program Files\Wireshark\tshark.exe" -r %1 -q -z http_req,tree >> %1_DIR\httpstats.%1.txt echo "#####HTTP SERVER TREE SECTION####" >> %1_DIR\httpstats.%1.txt "c:\Program Files\Wireshark\tshark.exe" -r %1 -q -z http_srv,tree >> %1_DIR\httpstats.%1.txt echo "##FINISHED PARSING###" Tshark Reference Links: http://www.packetlevel.ch/html/tshark/tsharkfilt.html Here is a quick layout of my home/lab network. Most of my analysis will happen within the 172.16 network. I am running a VMWare Server to 'serve' the Virtual image. The SState box is a workstation I have which runs a CoreRestore chip so the hard drive goes back to a normal state after reboot. This environment should give me a good playground for malware analysis, exploit stuff, packet analysis, and signature writing.
|
AuthorSecurity Researcher with about 20 years in the Computer Security Field. Going to talk even if no one is listening.. Archives
January 2022
Categories
All
|
||||||
| Mr Bartlett Blogs |
|


 RSS Feed
RSS Feed
