______________________________________________________________________________
From: <REMOVED>
To: <REMOVED>
Cc:
Date: Tue, 27 Dec 2011 09:16:59 -0500
Subject: 1144444.927
hi, nice day
hXXp://sebastienlarousse.teria.org/offer/newOffer.php?ekjprofiles=10
_______________________________________________________________________________
When I visit the link in my lab I am redirected to:
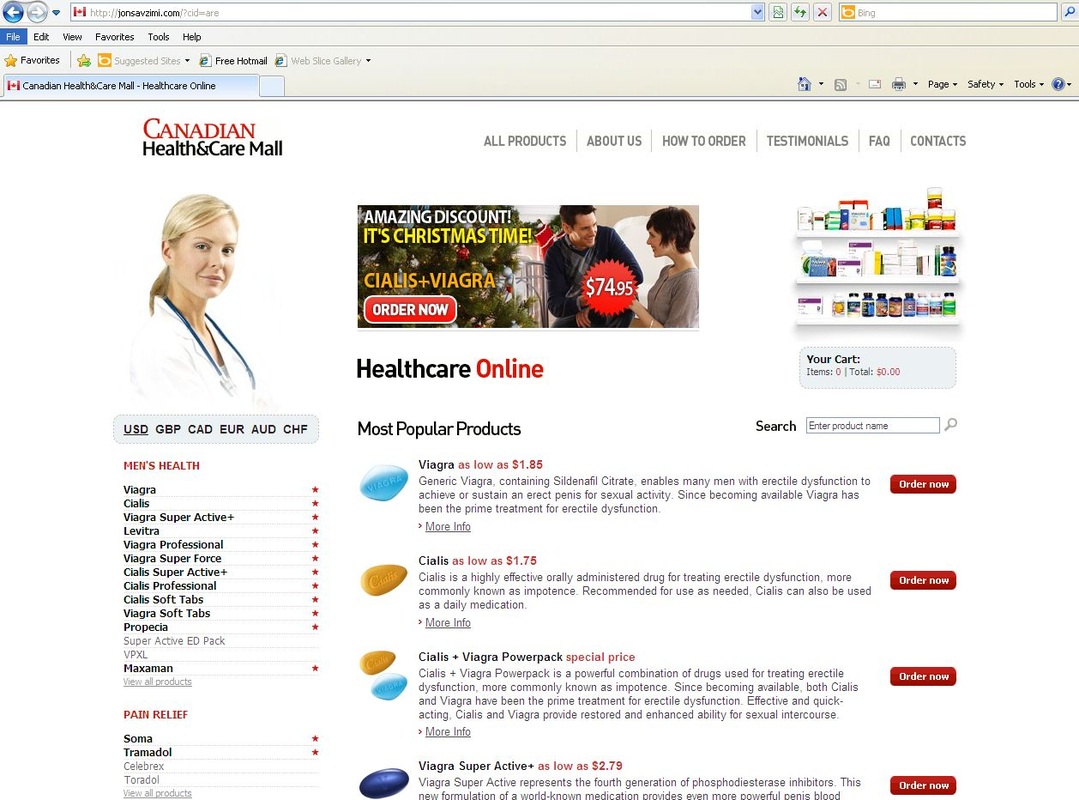
hXXp://jonsavzimi.com/?cid=are
Which looks like an on-line Pharmacy, where you can buy all the goodies; viagra, cialis...
It's using 2 names servers:
ns2.medicalpillshiv.com - which appears in multiple on-line malware analyzer reports.
ns1.uvqip.ru - which also appears in multiple on-line malware reports.
My advice when something like this happens to your account:
1. CHANGE your account password!! Then at least someone can't send emails directly from your account. (There are other ways to use your email address without having access to your account in some SPAM campaigns but that's another blog all together) Also look into enabling the 2-step verification
2. Take your machine off line and run an up-to-date ROOT KIT scanner against it. This will give you a good indication on whether your machine has some nasties installed on it. (The 'bad guys' might have brute forced the password on your 'on-line' account, but worse you could have a keylogger installed on your machine which has grabbed your password for the account and forwarded it out..) Here are some links for root kit scanners: http://www.sophos.com/en-us/products/free-tools/sophos-anti-rootkit.aspx , http://support.kaspersky.com/faq/?qid=208283363
Remember to change your on-line account passwords often and use STRONG passwords (here is a good video on creating passwords: http://youtu.be/Ah3gCnTi8b8)
Check your SENT FOLDER periodically to double check emails are NOT being sent from your account which you have NOT sent yourself.
And as always, KEEP YOUR MACHINE UP-TO-DATE with PATCHES (Operating System and Applications!)
PS. I'll be updating this blog once I analyze the network capture associated with this traffic.
mark


 RSS Feed
RSS Feed
